Key Takeaways:
- Most organizations are confident in recovery, but targets may not match business reality: 90% are confident they can meet defined RTOs, yet only 69% say those RTOs fully align with business continuity goals.
- Disruption is already happening and it hits customers and revenue: nearly 3 in 10 experienced a cyber incident causing downtime/data loss/disruption; among those, 42% saw customer disruption and 41% reported financial impact.
- Ransomware exposes the real resilience gap: of those hit, 56% faced encryption or exfiltration, yet only 28% fully recovered, while 44% recovered less than 75% of affected data.
- AI is amplifying risk faster than governance can keep up: 43% say AI adoption is outpacing security; 42% lack visibility into AI tools/models—reinforcing why resilience must combine visibility, enforced controls, proven recovery testing, and executive alignment.
Digital transformation, cloud adoption, and AI have increased the value of enterprise data and expanded the attack surface around it. Data moves across clouds, applications, APIs, models, and automated systems faster than most organizations can track.
That’s the paradox at the center of the Data Trust and Resilience Report 2026: despite rising complexity, most organizations believe they’re prepared.
The core theme of the report is simple:
Confidence ≠ validated recovery capability.
What we studied (and why it matters)
The Data Trust and Resilience Report 2026 is based on input from 900+ security leaders, spanning C-suite and frontline security roles, to understand how organizations are building (and measuring) data resilience in a world shaped by cloud, cyberthreats, and AI.
Key finding #1: The “confidence gap” is real (and it’s measurable)
Most organizations believe they can recover quickly after a disruption, but the data shows a gap between confidence and operational alignment.
- 90% of respondents say they are very to extremely confident they can recover within defined RTOs.
- Yet only 69% say those RTOs are fully aligned with their organization’s business continuity goals.
That difference matters because RTOs only protect the business if they reflect the reality of what the business needs. When recovery targets are set in isolation, or aren’t revisited as cloud architectures, SaaS dependencies, and AI-driven workflows evolve, teams can “meet the RTO” and still fail the business outcome.
What this looks like in practice:
- Recovery targets exist, but they’re outdated relative to new apps/data flows.
- Teams can restore systems, but not in the right order to resume critical operations.
- Backups and recovery tooling are in place, but restore performance and runbooks aren’t validated against business-impact scenarios.
Bottom line: A high confidence score is not the same as proven resilience. The organizations that close this gap treat recovery as a measured capability, not a belief.
Key finding #2: Real incidents are common and the business impact is significant
The confidence gap isn’t theoretical. The report shows that disruptive cyber events are already a lived reality for many organizations:
- Nearly 3 in 10 organizations experienced a cyber incident in the last 12 months that resulted in data loss, downtime, or business disruption.
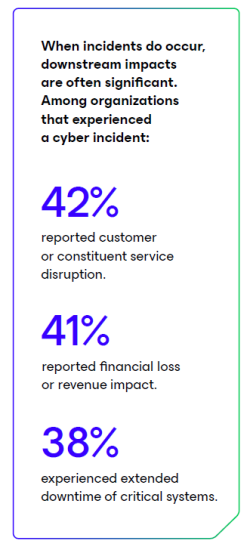
And when incidents happen, the consequences extend beyond IT metrics. Among organizations that experienced an incident, respondents reported:
- 42% customer/constituent disruption
- 41% financial loss or revenue impact
- 38% extended downtime of critical systems
This is why “we have backups” and “we have an RTO” aren’t enough on their own. If resilience isn’t validated end-to-end, across people, process, and technology, organizations can be operationally exposed even when they believe they’re prepared.
Key finding #3: Ransomware recovery is where optimism breaks
Ransomware continues to be one of the clearest stress tests of data resilience because it doesn’t just disrupt systems; it targets the organization’s ability to restore trust in its data.
Among respondents who experienced ransomware in the past 12 months:
- 56% reported attackers encrypted or exfiltrated data.
- Only 28% said they fully recovered all affected data.
- 44% said they recovered less than 75% of the affected data.
Those numbers highlight a hard truth: even when organizations survive an attack, many don’t return to “normal” in the way they expect. Partial recovery can mean permanent data loss, prolonged downtime, delayed customer commitments, and higher operational risk long after the incident is “closed.”
What this finding suggests: resilience isn’t just about having recovery technology. It’s about whether recovery is protected, practiced, and executable under pressure, when identities are compromised, systems are unstable, and decisions must be made quickly.
Key finding #4: AI adoption is outpacing risk visibility and governance
AI is changing how data is created, moved, summarized, and shared, often through tools and workflows that weren’t part of traditional security and compliance models. The report shows many organizations are adopting AI faster than they can govern it.
Key signals from the research:
- 43% say AI adoption is outpacing their ability to secure data and models.
- 42% report limited visibility into which AI tools/models are being used.
- 40% say their policies haven’t been updated for AI-specific risks.
- 25% cite unauthorized (“shadow”) AI tools as a primary concern.
This combination is a resilience problem, not just an AI problem. When teams don’t have clear visibility into AI usage, and policies and controls lag behind reality, it becomes harder to answer basic questions during an incident or audit, such as:
- Where did sensitive data go, and through which AI tools?
- Which teams approved (or didn’t approve) a given model or workflow?
- What data was used for prompts, fine-tuning, retrieval, or agent actions and is it recoverable and provable?
Key finding #5: Policy alone doesn’t reduce risk. Enforced controls do
Many organizations recognize AI-related risks, but the report indicates that having policies isn’t enough. Outcomes improve when policies are backed by technical controls that reduce data exposure and help enforce how data can be used.
One example highlighted in the report is data loss prevention (DLP):
- 48% of respondents say they have DLP in place.
And when DLP is in place, the report shows meaningful differences:
- Limited visibility into AI tools/models: 39% (with DLP) vs 45% (without DLP)
- AI adoption outpacing security controls: 38% (with DLP) vs 48% (without DLP)
The takeaway isn’t that DLP alone “solves” AI risk, it’s that enforcement changes outcomes. In practice, stronger resilience comes from pairing governance (what should happen) with control mechanisms (what can happen), plus monitoring and review loops that adapt as AI usage expands.
Key finding #6: AI governance ownership is fragmented (especially after incidents)
AI governance can’t work if no one clearly owns it. Among organizations that experienced a cybersecurity incident, responsibility for AI governance is spread across multiple leaders and models:
- 38% say AI governance is owned by the CISO
- 27% say it’s owned by the CIO
- 17% say it’s owned by a cross-functional committee
This fragmentation creates real resilience risks because AI-related decisions span security, IT operations, data/platform teams, legal/compliance, and the business. Without a clear operating model (who sets policy, who enforces controls, who validates recovery, and who reports risk), organizations can end up with:
- Policies that don’t translate into enforceable controls
- Gaps in visibility into AI tools/models and data flows
- Slower decisions during incidents (including what must be recovered first, and why)
What stronger-recovery organizations do differently: 4 capabilities linked to better outcomes
The report points to a consistent pattern: organizations with stronger resilience outcomes treat data trust and recovery as an operational capability, something they can measure, validate, and improve, not just a set of tools or policies.
Four capabilities show up as the foundation for stronger recovery:
1) Visibility into data and AI risk
Stronger organizations invest in understanding what data they have, where it lives, how it moves, and how AI tools/models interact with it. That visibility is what makes it possible to manage exposure, prioritize protections, and respond quickly when something changes.
2) Enforced controls (not policy-only governance)
Policies define intent. Controls shape reality. Stronger organizations back governance with enforceable safeguards (for example, protections that reduce data leakage and limit risky behavior), and they monitor for drift as AI and cloud usage expands.
3) Proven recovery (tested and validated)
Stronger organizations don’t assume recovery will work under pressure; they test restores, validate outcomes, and treat recovery drills as a regular discipline. This is where “confidence” turns into measurable capability.
4) Executive alignment on ownership and reporting
Resilience improves when there’s clear ownership for governance and recovery and when risk and readiness are reported consistently to leadership. That alignment helps prioritize funding, reduce ambiguity during incidents, and ensure recovery goals match business impact.
Key takeaway: when these four capabilities are present, organizations are better positioned to protect trust in their data and to restore operations when disruption isn’t optional.
The investment connection: measurement and reporting correlate with better outcomes
We are seeing a clear pattern: organizations that invest more in cybersecurity also tend to measure resilience more rigorously, and they’re more likely to communicate risk to leadership on a regular basis.
Budget direction is split
- 49% of organizations increased cybersecurity budgets.
- 51% kept budgets flat or decreased them.
Budget increases correlate with better measurement discipline
Organizations with increased budgets were more likely to track key readiness metrics, including:
- RTOs: 78% (budget increased) vs 56% (flat/decreased)
- Time to isolate/contain incidents: 47% vs. 36%
- Automated/orchestrated recovery: 32% vs. 14%
Monthly reporting to leadership is more common in higher-investment organizations
- Reporting cyber risk to the board monthly: 62% increased budgets vs. 47% who did not
- Reporting cyber risk to the C-suite monthly: 68% increased budgets vs. 49% who did not
Why this matters: resilience improves when it’s treated as a managed business capability. Measurement creates accountability, and consistent reporting helps leadership align priorities, fund gaps, and reduce the “confidence gap” before an incident forces the issue.
Standout stat: Full recovery doubles when budgets grow (correlation, not causation)
If you only remember one number from the report, make it this:
- Organizations that increased cybersecurity budgets were far more likely to fully recover all affected data after an incident: 40% versus 16% for organizations with flat or decreased budgets.
It’s important to be precise about what this finding does (and doesn’t) mean:
- This is correlation, not causation. More spending alone doesn’t guarantee recovery.
- But higher investment often comes with the things that do improve outcomes: better visibility, stronger controls, more frequent validation/testing, and clearer executive reporting.
In other words, the organizations that recover best tend to treat resilience as something they continuously fund, measure, and operationalize, not something they hope will work in a crisis.
Compliance is rising as a resilience driver (not just a checkbox)
The report suggests that resilience planning is being shaped by more than threat activity. Regulatory and compliance mandates are increasingly influencing how organizations design data protection, governance, and recovery.
When asked about emerging risks over the next 12 months, respondents highlighted:
- Cyberattacks: 36%
- Regulatory and compliance mandates: 33%
That proximity is telling: many organizations now view compliance pressure as nearly as consequential as threat pressure, especially as AI and cross-border data flows accelerate.
Data residency and sovereignty are shaping decisions
In addition, the report shows how strongly data placement is being driven by regulatory expectations:
- 58% say data residency and sovereignty is the most important factor in deciding where data is stored.
Why this matters for resilience: compliance requirements can dictate where backup data can live, how long it must be retained, and what must be provably recoverable. The stronger organizations treat compliance as a forcing function to improve discipline: aligning governance, controls, and recovery validation so they can demonstrate both protection and recoverability.
Get the full report (and turn these findings into action)
Reading the findings is useful. Operationalizing them is what improves outcomes.
Download the Data Trust and Resilience Report 2026 to benchmark your organization and walk away with clear priorities you can apply immediately, including the data behind the confidence gap, what differentiates stronger recovery organizations, and the governance and measurement practices that correlate with better recovery outcomes.
Download the full report: [https://go.veeam.com/data-trust-resilience-report ]
Next steps you can take this week
Use the report as a working plan, not a PDF to file away:
- Benchmark your recovery reality: compare your RTO confidence vs. business continuity alignment and identify where targets are outdated.
- Pressure-test ransomware readiness: validate what “full recovery” means for your most critical systems and whether restores are actually proven.
- Inventory AI usage and visibility gaps: document which AI tools/models are in use and where sensitive data could be exposed.
- Move from policy to enforcement: prioritize controls (like DLP) where governance exists but outcomes lag.
- Put metrics on the agenda: establish a monthly cadence for reporting readiness and risk to executives.
Related resources
- Inside the Economics of Cyber Extortion research report: https://www.veeam.com/resources/wp-cyber-extortion-report.html
- Demystify Regulatory Compliance: Standards, Frameworks and Recommendations: https://go.veeam.com/demystifying-regulatory-compliance
- This is the Wake-Up podcast: https://go.veeam.com/wake-up-podcast.html
FAQs
1) What is data resilience (and how is it different from backup)?
Data resilience is the ability to protect, govern, and reliably recover critical data and systems after disruption (cyberattack, outage, human error). Backup is one component; resilience also includes enforced controls, visibility, testing, and validated recovery.
- Backup = copies of data
- Resilience = proven ability to restore operations and trusted data within business targets (RTO/RPO)
2) How do you set and validate RTOs so they align with business continuity goals?
To align RTOs with business continuity, treat recovery targets as a business requirement and validate them with testing.
- Tier applications/services by business impact (revenue, safety, customer ops)
- Map dependencies (identity, DNS, networking, SaaS, data platforms)
- Define RTO + RPO per tier, then confirm tooling and staffing can meet them
- Run restore tests and recovery drills (including “worst-day” scenarios like compromised admin access)
- Review and update targets when cloud/AI workflows change
3) How can organizations improve ransomware recovery and avoid partial restores?
Improving ransomware recovery comes down to making recovery points survivable and making restores repeatable.
- Use immutable/tamper-resistant backups and keep at least one isolated copy
- Enforce least privilege + MFA, and separate backup admin roles from daily admins
- Monitor for backup deletion attempts, policy changes, and abnormal job failures
- Maintain documented runbooks and perform regular restore testing (not just backup success checks)
- Include all critical data sources (cloud, SaaS, and AI-related data stores) in scope so recovery isn’t incomplete