DATAAI RESILIENCE
Resilience to keep data trusted, identities protected, and AI safe.
Protect critical data, secure human and AI access, and recover clean, verified, and fast across hybrid, cloud, and
SaaS — so IT and security teams can keep business running through ransomware, disruption, and agentic risk.
SaaS — so IT and security teams can keep business running through ransomware, disruption, and agentic risk.
550,000+ organizations run on Veeam — including 82% of Fortune 500.
How it works
Recover clean across platforms,
not back into risk.
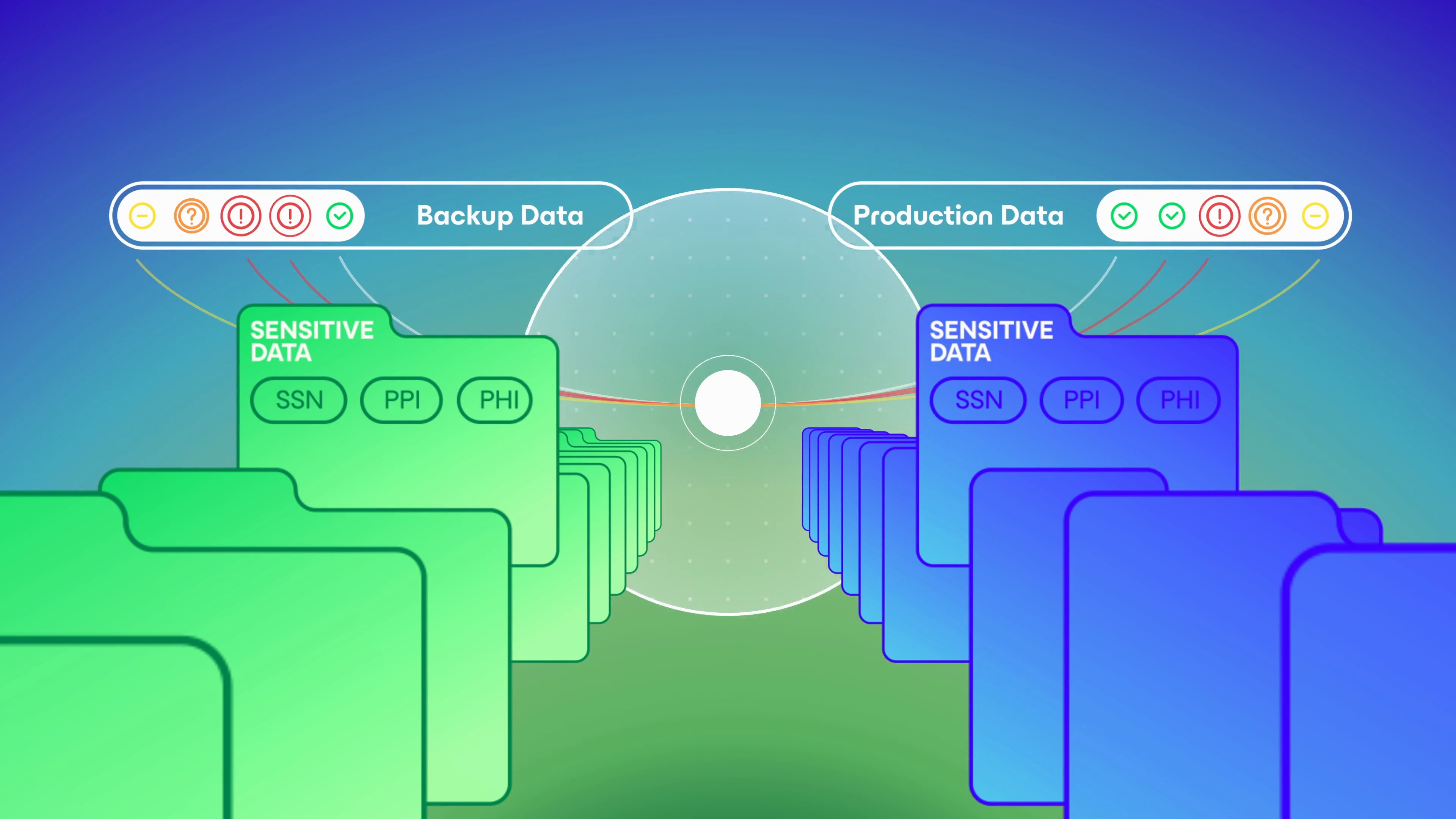
Threats are caught inline, data lands in three isolated resilience domains, and restore points are scanned
clean before you restore — to any supported target.
clean before you restore — to any supported target.


Portfolio
From SaaS to sovereign.
Built for how enterprises run.
Built for how enterprises run.
One portfolio, self-managed or delivered as a service, so protection fits every part of your estate.
On the roadmap
What’s coming soon.
Explore the leading platform designed to secure, scale, and simplify modern infrastructure.
Let's build your resilience plan.
Tell us what you're trying to protect. We'll point you toward the right product or help you choose between them. Book 30 minutes with a Veeam architect, tailored to your workloads and compliance needs.
Build Your Path to Trusted Data AI Resilience