Many organizations still understand cyber extortion primarily as a malware problem. Ransomware encrypts files, systems go offline, and a ransom demand forces a crisis response. That sequence still exists, but it does not fully explain many of the highest-impact incidents of 2025. Drawing on hundreds of engagements, Coveware by Veeam observed that initial access and attacker leverage increasingly shift toward people, process, and identity, with targeted social engineering emerging as a defining entry pattern. In many of these cases, the intrusion began well before ransomware entered the picture, and no threat actor group illustrates that shift more clearly than Scattered Spider.
Scattered Spider matters on its own terms, but its broader significance lies in what their tactics reveal where modern extortion is heading. This article uses the group as a lens for that larger shift. While directly attributable Scattered Spider activity appeared less visible after the first half of the year, the tradecraft associated with the group remained relevant to both attackers and defenders. The common thread is not a specific payload; it’s the ability to manipulate identity and administrative trust.
Identity is an attack surface
In practice, this often meant attackers calling help desks while impersonating users or IT support, manipulating MFA enrollment and reset paths, and exploiting the trust built into routine administrative actions, all before any data was encrypted or stolen. The greatest impact often came from the compromise of identity systems and workflows. Once an attacker can influence how access is granted, how changes are approved, and which actions appear legitimate, malicious activity can blend into ordinary administration with uncomfortable ease.
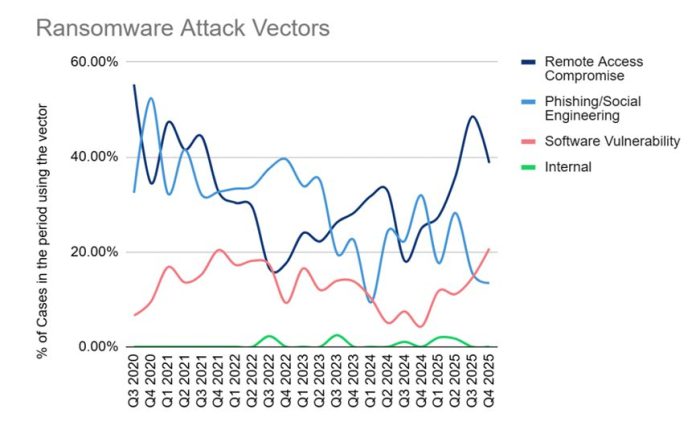
The help desk is one part of this attack surface. In many of the highest-impact 2025 cases, especially in mature enterprises, targeted social engineering remained one of the most effective entry paths. These campaigns played out across email, chat and collaboration platforms, SMS, and voice. Across the full year of reporting, initial access clustered around three dominant vectors: remote access compromise, phishing and social engineering, and software vulnerability exploitation. In each case, attackers sought a path through trusted systems, approved workflows, and privileged actions. They leveraged the authority of the person they manipulated, then moved through help desk resets, MFA enrollment, remote support, and routine approvals to gain privileged access, deploy tooling, and expose data.
That makes this a different problem from the older phishing story many leaders still have in mind — the issue is broader than a suspicious email or stolen password and has extended well outside the inbox. Phishing has been absorbed into a wider category of trust exploitation, one that manipulates OAuth grants, integrations, remote support tooling, and identity workflows to establish durable access that looks legitimate to defenders. The intrusion may unfold through approved actions, valid sessions, and recognized tools, which helps explain why these incidents can be difficult to spot early, highly disruptive once they take hold, and challenging to remediate.
This is why the issue belongs in executive conversations alongside awareness training and service desk coaching. Many of the weak points are in identity governance and in the operating procedures of IT, service desks, and business teams, well beyond endpoint or perimeter controls. The risk extends to third-party providers and contractors as well, especially when they sit inside the same workflows with standing access, weaker verification standards, or less mature monitoring. If a partner can reset access, approve changes, administer tools, or influence identity-related workflows, that relationship is part of the threat model whether the organization has formally accounted for it or not.
Restoring trust takes longer than restoring systems
The consequences rarely end with the initial compromise. One of the clearest observations about Scattered Spider is that the longest tail in recovery is often the work of restoring confidence in identity across the organization: credential resets, access revalidation, device trust rebuilding, and governance hardening. If attackers have manipulated identity pathways and administrative trust, technical restoration alone does not close the gap they opened. The real question is whether the environment can be trusted again once a threat actor is thoroughly entrenched.
Identity and access management is a critical Tier 0 dependency that underpins the entirety of the environment. Restoring identity to a trusted baseline is a necessary predicate before any application or database restoration can truly begin. The threat actor needs to be eradicated to ensure safe and secure recovery.
That recovery challenge is further complicated by a broader pattern observed throughout 2025. Attackers increasingly contested recoverability by compromising backup-related identities and tampering with backup configurations, schedules, policies, and objects in ways that may not be discovered until the time of restoration. This shifts the question from whether backups exist to whether recoverability can be proven under adversarial conditions and underscores the importance of securing the backup infrastructure and configuration beyond immutability of the backup itself.
What this means for leaders
That leaves leaders with a practical question: Can you reliably recover trusted identity control if privileged access is compromised, and can you prove the recovery mechanism is complete and secure? The answer depends on whether you can rapidly re-establish authoritative control of IAM/SSO/PAM/MFA and directory services, invalidate compromised sessions and tokens, and re-issue privileged access through clean administrative pathways.
It also depends on whether your recovery procedures hold under pressure, are fully documented and testable, and extend to third parties and managed providers operating inside the same identity workflows. In this environment, resilience depends on identity recovery, workflow governance, and recoverability working together — not on malware detection alone.
Scattered Spider is a useful case study because it gives this shift a recognizable face, but the lesson extends well beyond any one group. The broader 2025 conclusion is that cyber extortion attacks are no longer best understood only as a malware problem or a negotiation problem. They are increasingly an identity, resilience, and governance problem.
When attackers can turn routine support actions into privileged access, the help desk and other administrative workflows become control points for whether the business can recover at all. The organizations that perform best will be the ones that treat identity as a recoverable system: they harden and govern high-risk administrative actions, maintain clean pathways to re-establish privileged control, and rehearse identity recovery end-to-end so they can restore access with confidence that compromised credentials, sessions, and trust relationships have been fully and safely reset.
For insights from the frontline of cyber extortion, click here.
