The release of Anthropic’s “Claude Mythos Preview” suggests a potential shift in vulnerability discovery velocity for enterprise security. AI has held the potential to be a tool that would “help” defenders. But as recent weeks have shown, Mythos isn’t just a helper; it is a potential catalyst for what M.G. Siegler at Spyglass calls a “casual catastrophe.” It is a model that finds issues not because it is a force of superintelligence in the sci-fi sense, but because it operates at a scale of intelligence and time that humans simply cannot match. For enterprise security teams, this shift transforms the mundane task of patch management into a high-stakes race where hours matter.
Old Bugs Erode Trust in Vetted Code
Security teams have historically prioritized patches for new vulnerabilities. The logic was often implicit: older, widely used code was assumed to have lower marginal risk because it had been exercised and reviewed repeatedly. Agentic discovery tools now challenge that assumption. In its first few weeks, the Mythos model was reported to have identified a 27-year-old vulnerability in OpenBSD and a 16-year-old flaw in FFmpeg — in code that had already passed extensive automated testing.
As Siegler points out, these aren’t issues humans couldn’t find; they are issues humans wouldn’t find. Humans lack the patience to scrutinize every line of a twenty-year-old dependency. Models can. For the enterprise, this means your “technical debt” is no longer just a performance drag — it is a live, automated firing range for agentic AI. The silver lining, at least for now, is that the operational cost of finding the OpenBSD vulnerability was still pretty high (estimated to be about $20,000), and the cost of acquiring these vulnerabilities has not collapsed at the same rate that the speed of discovery has.
The Collapse of the Deployment Window
Patch windows used to be grace periods. A vulnerability would be announced (a CVE), and teams had days or weeks to test and deploy a fix before a reliable exploit was developed.
With agentic tools, patch-diffing automation, and LLM-assisted exploit development, that patch window is tightening, sometimes dramatically for high-value or internet-facing targets. As soon as a patch is publicly available, automated tooling can compare the “before” and “after code, deduce the vulnerability, and generate a working exploit in minutes to hours in some cases. Additionally, unlike human attackers who might stop at one entry point, automated tooling can identify additional vulnerabilities in a single system and autonomously chain them.
AI-driven analysis is shrinking the window between patch release and exploit development, increasing the importance of fast, risk-based patch deployment. If your deployment cycle takes 48 hours, you may already be effectively too late. Enterprises must target patching velocity that is as fast and autonomous as the attacks themselves for the highest-risk classes (e.g., internet-facing, identity, remote management, and externally reachable third-party components).
The New “Black Box” Attack Surface is Hardware
As enterprises rush to build out the infrastructure for 2026-era AI, they are introducing increasingly heterogeneous platforms — accelerators (GPUs/TPUs), ARM-based hosts, and specialized NIC/DPUs and firmware-managed components.
This creates a visibility gap. Attackers are more inclined to target firmware and management-plane components because they can bypass OS-level controls and complicate detection and recovery. These vulnerabilities are “silent” and often bypass traditional OS-level security patches. Patching a firmware vulnerability often requires a reboot or cold start of hardware clusters. In an era of 24/7 AI-driven operations, the downtime required to patch hardware is often seen as more expensive than the risk of the bug itself — a gamble economically motivated adversaries may exploit.
Vibe Coding and the Dependency Sprawl Problem
Another pressure point is the way we build software. We’ve entered the era of “vibe coding,” where developers use AI to generate entire modules from “vibes” or high-level prompts. Productivity rises, but so does dependency sprawl: AI-assisted builds can introduce obscure open-source components and transitive (“shadow”) dependencies that security teams don’t realize are in production. Just as importantly, AI-generated code often ships with less shared understanding, reducing the defender’s traditional advantage of knowing how the system is supposed to behave.
The Mythos Quandary is that we’re trying to solve a machine-speed problem with a human-speed process. Enterprise security has to move toward faster, higher-confidence patch deployment for defined high-risk classes. Where patch SLAs can’t meet exposure timelines, compensating controls and virtual patching can buy time by blocking known exploit paths — but they do not remove the need to patch.
As it relates to ransomware, the probability of a true systemic extortion event occurring has increased dramatically. WannaCry and NotPetya are reminders of how quickly vulnerability-driven disruption can go systemic. Mythos-class capabilities in the hands of cyber criminals are a future that we should treat as a plausible near-term scenario and plan accordingly, without assuming every actor will have equal capability.
What comes from this is uncomfortable, but clear. In the agentic AI era, patching is no longer a maintenance function, it’s a race condition. The organizations that hold up will be the ones that can ship fixes fast for the few systems that truly matter, surround everything else with compensating controls that actually reduce exposure, and maintain enough software and asset visibility to know what they’re defending. The rest will be forced to make high-stakes decisions, under outage pressure with imperfect facts, on an adversary’s timeline.
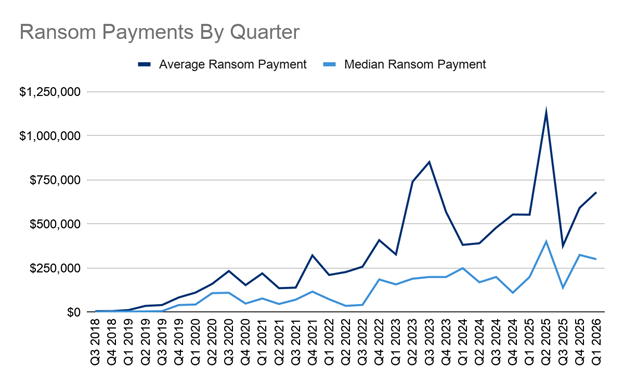
Ransom Payment Amounts in Q1 2026
- Average — $680,081 (+15% from Q4 2025)
- Median — $300,750 (-7% from Q4 2025)
The 15% increase in average payments to $680,081 highlights the continued success of sophisticated groups targeting large enterprises with data-exfiltration-only incidents. Conversely, the 7% dip in median payments to $300,750 suggests that mid-market and smaller organizations are becoming more resilient, likely due to improved backup protocols and a firmer refusal to pay for data exfiltration alone.
Most Common Ransomware Variants in Q1 2026
|
Rank |
Ransomware Type |
Market Share % |
Change in Ranking from Q4 2025 |
|
1 |
Inc Ransom |
13% |
New in Top Variants |
|
1 |
Lone Wolf |
13% |
+2 |
|
2 |
Akira |
12% |
-1 |
|
3 |
Anubis |
8% |
New in Top Variants |
|
3 |
Qilin |
8% |
-1 |
|
3 |
Shiny Hunters |
8% |
+3 |
As with all Coveware by Veeam data, these figures reflect first-hand, observed casework. The most common groups carrying out cyber extortion attacks in Q1 2026 represent a dichotomy of extortion strategy. INC, Akira and Qilin remain the most active encryption-focused groups, while “Lone Wolf” operators and brands such as ShinyHunters account for a meaningful share of overall extortion activity. Where ShinyHunters- and Lone Wolf-style campaigns skew toward data-exfiltration-only pressure, a disproportionate share of cases that ultimately result in payment continues to concentrate among encryption-led groups. Across both models, business interruption remains the strongest driver of payment outcomes.
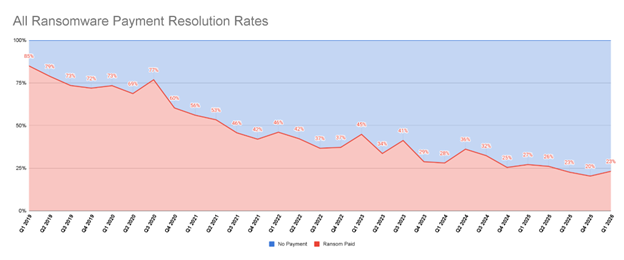
Overall, companies continue to resist cyber extortion pressure. Payment rates across Coveware by Veeam’s managed cases ticked up slightly to 23%. Despite this trend, we continue to see incidents where clients receive biased or miscalibrated guidance driven by weak threat actor attribution and stale intelligence. Attribution of loosely affiliated “lone wolf” operators remains especially challenging, and maintaining accurate, current intelligence is now table stakes for defensible incident response decision-making.
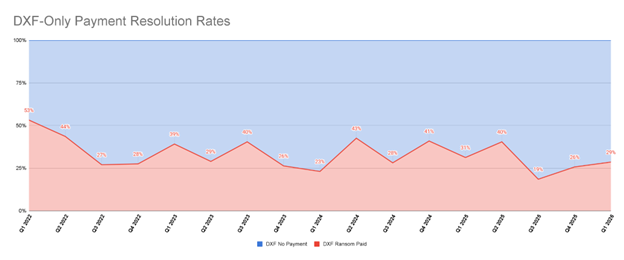
Data-theft-only payment rates continue to show quarter-to-quarter volatility, but they remain structurally low, reinforcing that data-theft-only extortion converts poorly for threat actors. Such sustained suppression reflects a meaningful posture shift: enterprises increasingly begin data theft incidents from a starting posture of non-payment by default.
Practically, this supports an executive stance that payment should be treated as an exception rather than a primary mitigation lever. This is especially true as experience continues to show that payment rarely delivers durable risk reduction — data deletion promises are unverifiable, data may be retained or resold, and payment does not reliably prevent future targeting or secondary extortion. A critical data point we continue to emphasize is that re-extortion (where victim being extorted for the same dataset) and default (the release of data despite assurances it would be destroyed) can take months or even a year to materialize. The short-term “promises kept” cannot and should not be characterized as evidence that the bad actors are honoring their word.
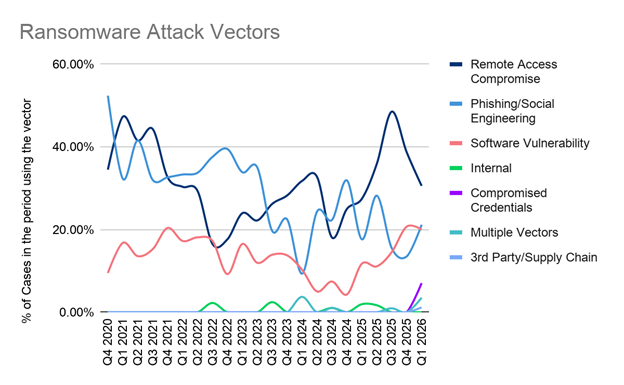
Most Common Ransomware Attack Vectors in Q1 2026
Initial access patterns in Q1 2026 continue to consolidate around remote access compromise. But “remote access” increasingly means SaaS and identity-backed pathways (SSO, OAuth grants, connected apps, and administrative access) rather than just legacy VPN/RDP. In practice, many intrusions look more like legitimate logins followed by persistence than like break-ins. That convergence matters operationally: initial access and persistence are effectively the same problem, because threat actors are aiming to log in and stay long enough to escalate privileges, move laterally, and execute extortion objectives.
Within that context, phishing and social engineering remains a major mechanism. These attacks increasingly target help desks and identity recovery workflows, and they can remain low-signal until a meaningful change occurs (new enrollments, privilege changes, or data access or exfiltration). While less frequent than the final vector in appearance, successful campaigns often culminate in outcomes that present as remote access compromise. As such, detection priorities shift to abnormal admin actions, unusual MFA resets or enrollments, new OAuth grants and connected apps, impossible travel, unfamiliar devices or geographies, and anomalous support activities.
Finally, software vulnerability exploitation remains lower-frequency but higher-consequence, and continues to trend upward — particularly in internet-facing appliances and management planes, where patch lag and migration hygiene gaps create fast conversion opportunities.
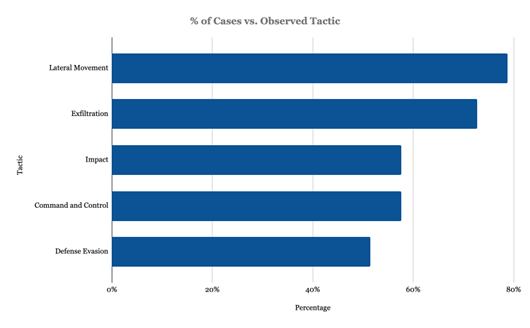
Most Common Ransomware Tactics in Q1 2026
In Q1 2026, the top observed tactics reinforce a familiar reality: most cyber extortion events of impact are still hands-on-keyboard operations where attackers prioritize the ability to move, stage, and maintain control long enough to create leverage.
Lateral Movement remained the most consistently observed tactic (79%). That consistency matters: east‑west movement is the operational backbone of many intrusions, and it often rides on legitimate administrative paths that can blend into normal activity. The practical implication is unchanged: organizations that can detect and contain lateral movement quickly tend to preserve more recovery options and maintain better negotiating leverage.
Exfiltration continued to function as the primary leverage mechanism (73%), not merely a precursor to encryption. Even when exfiltration appears “lower” in observed telemetry, it often reflects visibility limits or attacker speed rather than reduced intent. Treat data theft as an executive risk issue as much as a technical one, because attackers do.
Impact rose into the top three (58%), aligning with what leadership experiences most acutely: business interruption is frequently the defining feature of the event. This category is also sensitive to evidence capture and logging quality, so the ranking should be read as directional rather than absolute. The decision implication is that recovery planning and decision authority matter as much as detection.
Command and Control also climbed into the top five (58%), suggesting more cases where responders can directly observe active operator connectivity. Disrupting command and control can reduce attacker tempo, but it can also change adversary behavior, so containment needs coordination and clear executive decision paths.
Finally, Defense Evasion remained a core enabling tactic (52%). A lower rank does not mean it’s less important; it often reflects what can be observed, especially when evasion succeeds. The control message holds: identity gaps, endpoint coverage gaps, and logging blind spots are still the seams attackers hunt first.
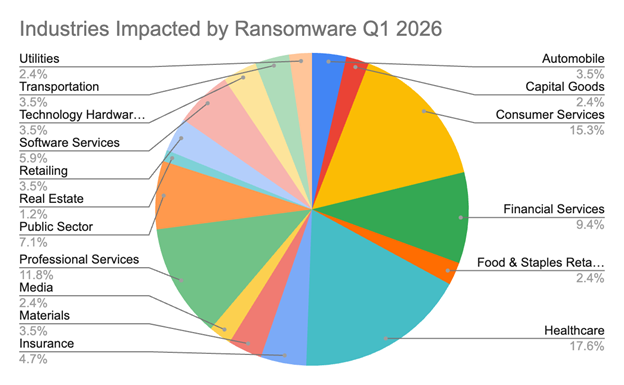
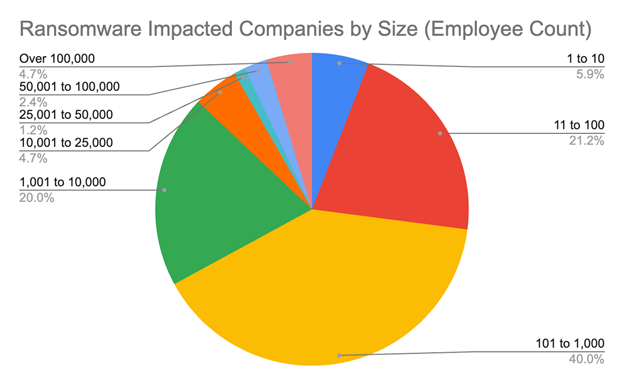
Most common Industry and Company sizes impacted by Ransomware in Q1 2026
While Healthcare (17.6%) and Consumer Services (15.3%) represent the largest shares of ransomware impact in Q1 2026 — reflecting low tolerance for downtime, high density of sensitive data, and clear extortion leverage — Professional Services (11.8%) and Financial Services (9.4%) underscore continued attacker focus on “data-rich” sectors. Together, organizations handling sensitive client and regulated data make up 32% of all attacks. Attackers prioritize these because the threat of leaking client data (like legal records or financial statements) is often more compelling than the encryption of the systems themselves. Must-Operate organizations like Public Sector (11%) and Healthcare are targeted because they provide essential services. When a school district or a hospital is hit, the pressure to pay is driven by public safety and continuity rather than just profit. While there was a short-lived post-Colonial Pipeline trend of ransomware groups maintaining “industry exemption” lists, that practice has largely dissolved — most RaaS groups now impact healthcare and critical infrastructure indiscriminately, alongside other common sectors.
The 11–100 and 101–1,000 tiers account for two-thirds of all attacks. Ransomware-as-a-service (RaaS) affiliates are finding the highest “Return on Investment” (ROI) by targeting smaller organizations with low cost, low payout, but high probability of payout attacks. Only 5% of victims have over 100,000 employees. This explains why the Average Payment ($680k) is rising even though the Median ($300k) is falling.
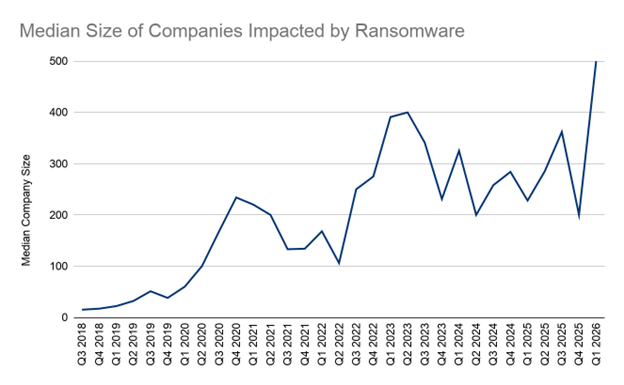
Median Size — 500 employees (+150% from Q4 2025)
The observed increase in median victim size is driven by a parallel surge in targeted, big-game-hunting attacks by mainly data-theft-focused actors. In quarters where opportunistic RaaS groups have controlled the highest market share, we see commensurate decreases in median company size.