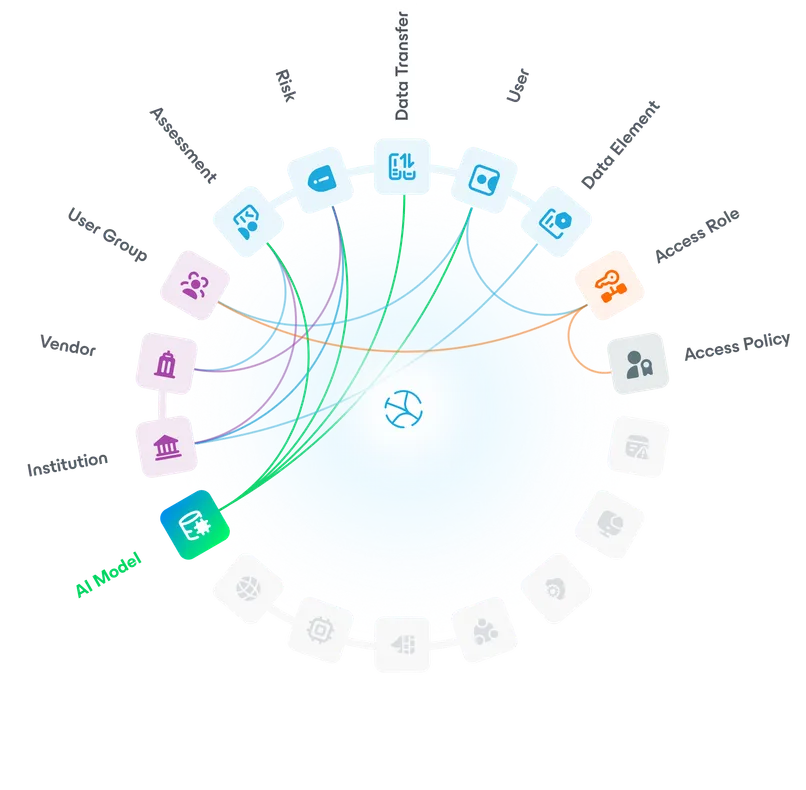
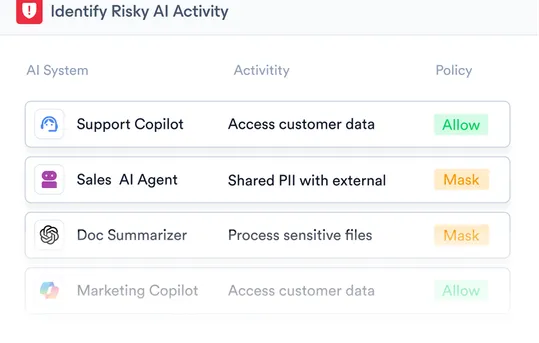
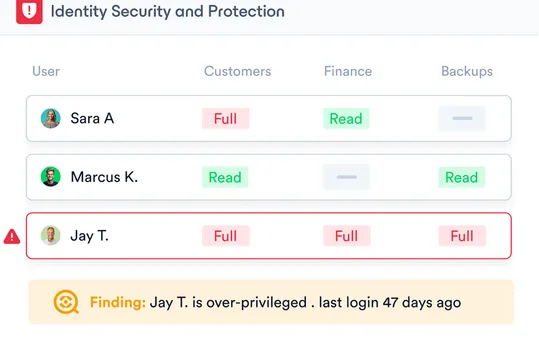
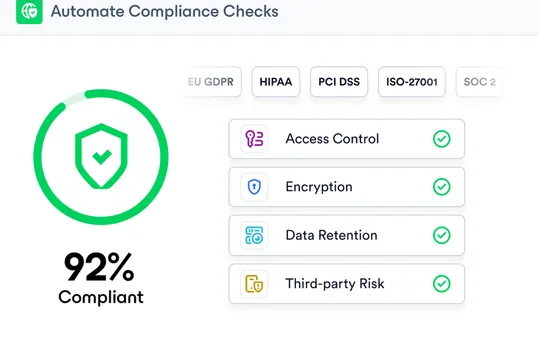
Continuously discover and classify sensitive data, and identify where it is exposed, over-shared, or at risk so you can act before it becomes a problem.
- Identify exposed data, public sharing, and excessive access
- See high-risk scenarios created by combinations of sensitive data, access, and activity
- Prioritize and remediate high-risk data exposures