A long time ago in a galaxy far, far away…. Wait, was it just 30 years ago? Ransomware is so common that we tend to think that it was always with us. Well, it’s just 31 years old but has caused numerous amounts of damage already — even though there’s still a moment of stunned incredulity when people first hear about ransomware.
This blog post will walk you through basic concepts and principles: What is ransomware? How does it infect your computer? And what is the impact on your business?
First ransomware attack in history
Back in 1989, evolutionary biologist Joseph Popp wrote “AIDS Trojan,” the first known malware that was an early example of a class of malware known as “ransomware.” AIDS Trojan was introduced into systems through a floppy disk, which Popp simply sent to a mailing list of attendees of the WHO International AIDS Conference. Just imagine: 20,000 infected diskettes were distributed! Joseph Popp was eventually caught, but could he imagine at that point in time that he started a new era of ransomware?
So…what is ransomware?
Speaking about the definition, I would put it in simple words: Ransomware is a form of software that is created with malicious intent and puts user’s files into code. It stands to mention that ransomware works by using file encryption, one of the most crucial tools in computer security. Some ransomware actors behave differently however, such as deleting files, encrypting applications (such as SQL Server) or uploading data to extort the organization. Ransomware will typically get access through insecure remote access, OS vulnerabilities, software downloads or email attachments.
How the ransomware process works
Alright, we get it — ransomware encrypts files on computers. But how does this happen?
Apart from the code and encryption algorithm, there’s always social engineering tricks involved.
I’m a big fan of the Mr. Robot series, which talks a lot about building an emotional connection with victims first before hacking them and encrypting their data. Sometimes, attackers even get in touch with the target on a social network and start a conversation with the target there. Step by step, the hacker gains the victim’s trust and then uses that trust to get access to private, sometimes even sensitive, data, like passwords or bank account details.
Probably not in such scale, but the same logic is being used with ransomware: you open email from someone you trust, friend, any legit organization, etc.; you receive intimidating messages that your computer just got infected (still emotional connection, huh?), so you click the link and here you go. Download completed. Ransomware is on your computer! But let’s dig deeper into the ways your computer can get into this trouble — as aware means armed.
First ransomware scenario: Malicious emails
 | User receives email with file attachments or links in the email body. Even though most emails like this will go to the spam folder, some of them can sneak into your inbox. |
 | User downloads file attachment or clicks the link. The process of ransomware installation has now started. |
 | Ransomware starts encrypting the data you have on the computer: photos, documents, PDFs, everything you got there. |
 | Now’s the time instructions show up and tell the user how to make a payment to the attacker to get the decryption — and it could be thousands of dollars! |
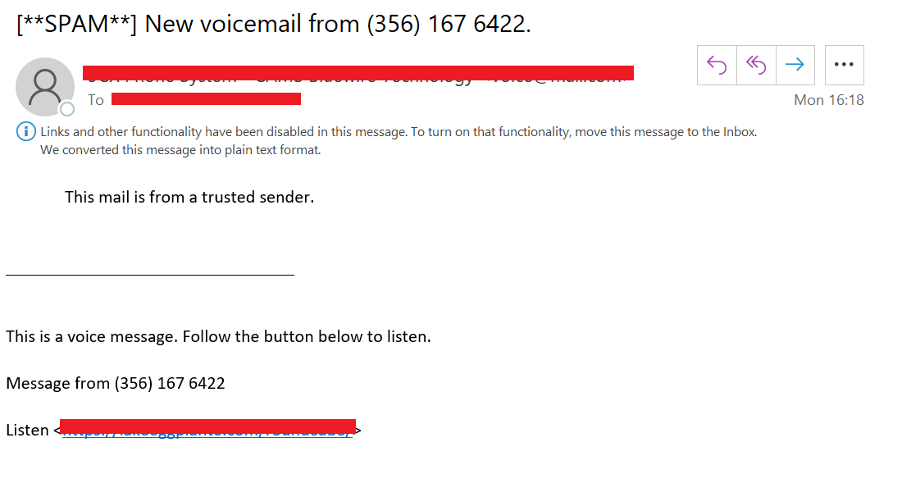
Below is an example of spam and probably malicious email. I can’t tell for sure if the link in the email body will download ransomware, but I don’t want to tempt fate (and look at the note on “trusted sender!”).
Second ransomware scenario: Browser and exploit kits aka malvertising
 | User clicks on online ads in browser and system redirects user to compromised website. |
 | Usually, attackers make sure to create these compromised websites to look legit, so it may take awhile for your antivirus and security system to identify exploit codes hidden there. |
 | Exploit kit starts examining your computer and launches some Java or Flash software to find any possible vulnerability. And if such vulnerability is found — ransomware will be placed into your computer. |
 | Ransomware will encrypt all the data saved on your computer’s hard disc (the same way as with the malicious email scenario). |
 | Instructions won’t take long, and you will have to pay the attacker again. |
Always keep in mind that payment doesn’t ensure that you get access to your files back. This only ensures that ransomware attackers will get your money — and that is it!
Who is the target audience of ransomware?
The answer is everyone.
Ransomware can be aimed at both individuals and businesses of any size. Every organization is at risk — whether you’re a small business or an enterprise. There is no limitation and again, every industry can be damaged: education, government, healthcare, retail, finance…if you think you’re not on the list — you should know that you are, as ransomware is a real threat and can lead to negative consequences.
The impact of ransomware on businesses
What about business impact? Impact IS huge.
In Q4 2019, the average payment for a ransomware decryption key went up by 104% to $84,116, up from $41,198 in Q3 of 2019. Payment doesn’t guarantee that you will restore access to data. This doesn’t even guarantee that your computer isn’t infected anymore.
Ransomware can be devastating, and the recovery process won’t be easy and may require additional resources.
Here are the key risks associated with ransomware:
- Data loss — temporary or even permanent
- Complete shutdown of business operations
- Financial loss due to disruption and downtime
- Financial loss associated with remediation efforts
- Company’s reputation
When ransomware hits — it’s a company-wide emergency; it is a disaster which needs to be recovered.
Protection against ransomware attacks
The best way to protect against ransomware is to prevent it from happening.
Back up your data, educate your business administrators on ransomware and invest in a good cybersecurity solution.
Talking about data protection, Veeam provides you with 100% ransomware-proof backups with S3 Object Lock functionality and immutable backups. To make the data immutable, Veeam Backup & Replication uses the Object Lock technology provided by Amazon and some S3-Compatible providers. If you haven’t yet tried the #1 modern data protection platform, download a FREE trial here.
If you’re ready to take it to the next level and want to know more about ransomware, I encourage you to check out the Beat ransomware: Education, Implementation and remediation with Veeam white paper and Winning the War on Ransomware podcast by Rick Vanover below to learn more practical steps organizations can take to protect data and avoid being in a situation where data loss or ransom payment are the only options.
Helpful ransomware prevention resources:
- Identify and protect yourself against ransomware
- Try our Ransomware Prevention Kit
- Read Beat ransomware. 3 Ultimate strategies white paper
- Watch 3 Ultimate Strategies for Ransomware Prevention webinar