- Veeam Data Platform
- Backup & Recovery
Veeam Backup & Replication
Backup Built to Protect, Recovery Built to Perform
- Backups are your last line of defense
- Broad workload and cloud coverage
- Hardened, Zero Trust controls with immutability
Benefits
Secure From the Start,
Recovery Assured
From Threat Detection to Rapid Recovery
Recovery Objectives On Time and On Target
Ransomware Protection Built to Last
Hybrid Cloud Protection Without Limits
Backup and Recovery That Stand Up to Malware
Malware often targets backups. Protect yours with immutable storage, verified restore points, and clear access controls to ensure resilience under pressure.
of orgs experienced at least one malware incident in the past year
saw backup repositories targeted during malware incidents
used immutable repositories or services before restoring
had a predefined chain of command for incident response
Sources: From Risk to Resilience: 2025 Ransomware Trends and Proactive Strategies
Capabilities
Keep Your Data Safe, Recoverable,
and Compliant
Pre-Built, Hardened, Predictable
Proactive Threat Mitigation
Verify Security and Compliance
Put the Spotlight on Malware
Embrace Data Portability
Highly Available
Available Anywhere
Secure Cloud Storage
AWS, Azure, and Google Cloud Backup
AI-Powered Assistance
Get a Second Opinion
Guarantee Survival
Recovery Rehearsed.
Resilience Proven.
extend multi-cloud protection,
and simplify backups.
HOW IT WORKS
Protect, Respond, Recover
Recover or Migrate to a New Hypervisor
See how you can move workloads to a new hypervisor with a few simple clicks.
Straightforward Recovery to Microsoft Azure
Whether it’s Microsoft Azure or another public Cloud, Veeam can provide you with a straightforward path.
Configure With Confidence and Streamline Your Security Posture
Leverage AI to find the answers you need while alerting you to the threats you may not know about.
Veeam Software Appliance
Your Fastest Path to Veeam Data Platform
Smooth deployment, secure from day one, managed from anywhere

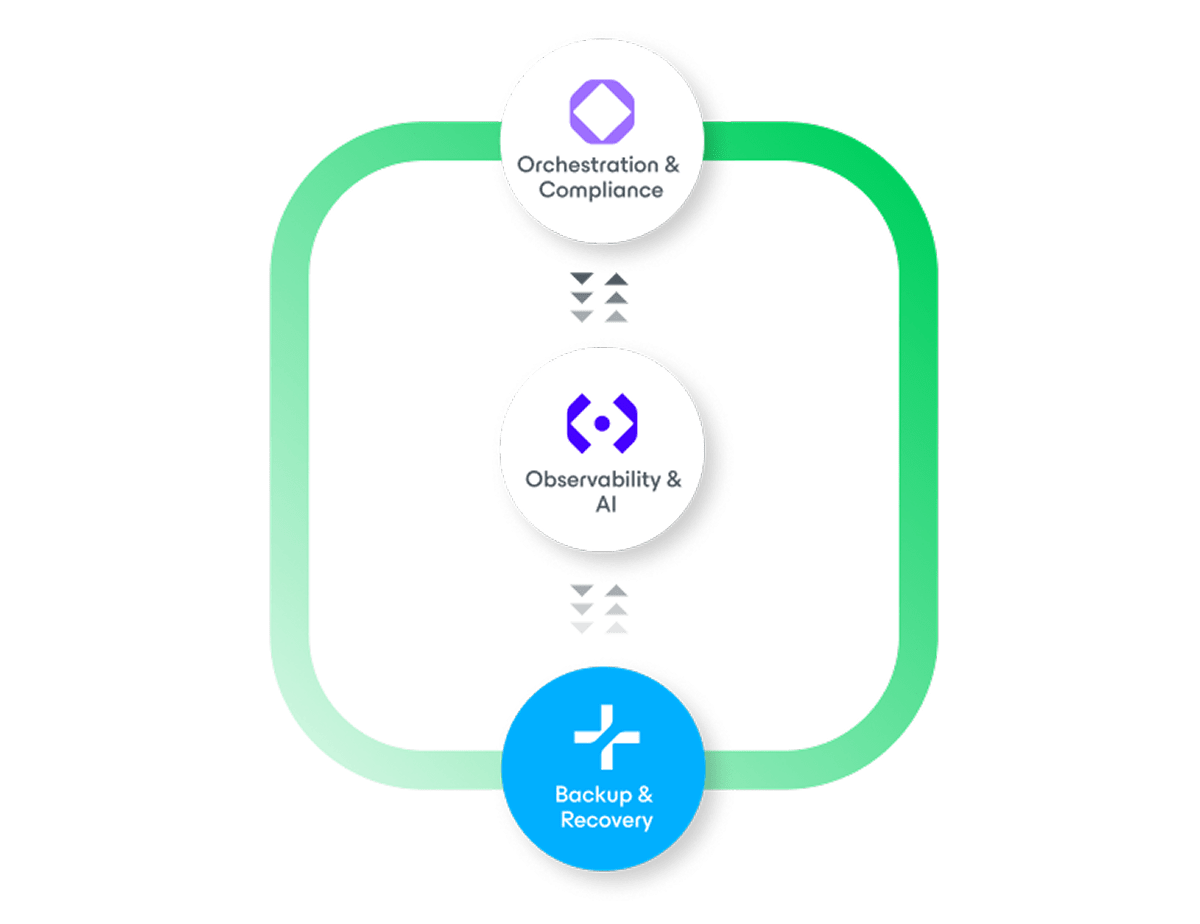
Platform Editions
True Data Resilience
Available in three comprehensive enterprise-grade editions — our most powerful premium option delivers the complete, secure protection and best-in-class orchestration that can only be achieved with Veeam Data Platform.
Foundation
Resilience
Resilience
Add On
Add On
Add On
Add On
Add On
Add On
Cloud Storage
Veeam Data Platform + Veeam Vault
- Data secured
- Operations simplified
- Costs controlled

FROM RANSOMWARE TO RECOVERY
Data Trust and
Resilience Report 2026
Insights to reach data trust and recovery goals faster
Managed Services
Check Out Our Customer Ratings
Resources
Backup and Recovery
Insights & Trends