Beyond traditional backup use cases, one of the most important capabilities Veeam Backup & Replication provides you as a customer is the ability to proactively leverage data. It also allows you to be smarter about what you do with the gold mine of data you have wrapped up in backups that are sitting idle and to improve operational efficiencies, increase speed to market and even leverage existing data to improve compliance and security.
Veeam Backup & Replication Update 4, along with a huge payload of other features, focuses on the leveraging of data and transitioning from being reactive to becoming more proactive with this valuable resource. This proactivity comes in the form of our new Veeam DataLabs. A few of Veeam DataLabs’ capabilities have been customer favorites for years, including SureBackup and SureReplica to verify recoverability, as well as On-Demand Sandbox to speed up application deployment and address several DevOps and Dev Test concerns. Now, Update 4 introduces Veeam DataLabs Staged Restore and Veeam DataLabs Secure Restore to address compliance and security use cases as well. Find out more about Veeam DataLabs.
Veeam DataLabs Staged Restore
What business can afford a data breach? Today, a breach often includes a guaranteed barrage of negative publicity, loss of trust from loyal customers, as well as the possibility of a decrease in future business, not to mention, fines!
According to a recent study, the average total cost of a data breach is $3.86 million, which is a 6.4% increase over 2017 (Source: 2018 Cost of a Data Breach Study: Global Overview, July 2018, conducted by Ponemon Institute LLC). This is why our first and most important new Veeam DataLabs use case focuses on GDPR and Article 17 (the right to erasure). This article applies to many of our customers who hold data from European citizens (regardless of their organization’s geographic location) and therefore must adhere to new data-compliance regulations or face a fine of up to 3% of their global turnover.
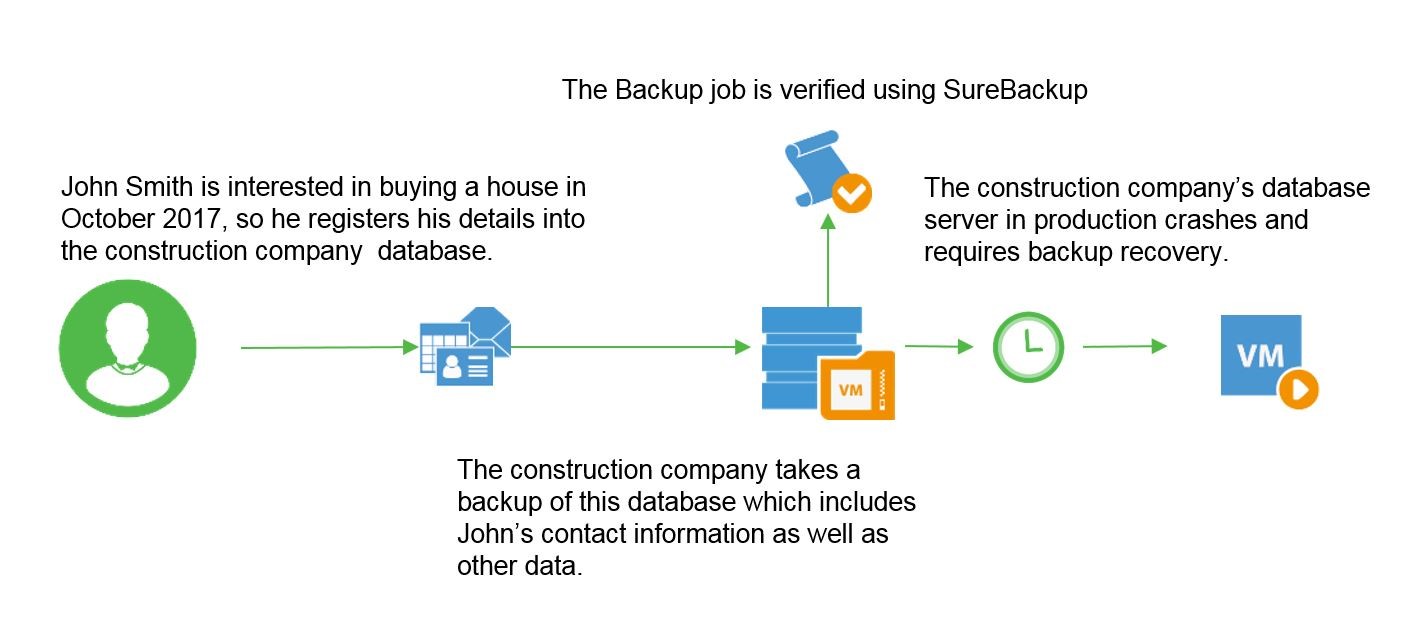
In the event that you lose critical data in production and are forced to restore the data, we are hopeful that backups exist, which have been tested with SureBackup to verify that the VM, application and OS are in good working order. SureBackup provides Veeam customers with peace of mind and reassurance that their backups have been successfully booted and tested for recoverability. However, while verifying backup recoverability is an effective first step to recovery, as of May of 2018, most businesses still need an effective way to also ensure compliance during this process. What if the backup being restored contains sensitive data protected by GDPR regulations? Leveraging the capabilities of Veeam DataLabs Staged Restore helps simplify this process.
Let’s look at this process before and after the introduction of GDPR and use a construction company as an example. Suppose this company is contractually required to keep data related to a new housing development for 25 or more years. This data may include supporting emails, contacts, reports, quotes, inquiries, etc. associated with the build. Eventually, the company may use this data to determine which showrooms were most popular, which customers preferred specific designs, etc. to improve their business and marketing tactics. In this case, the company would retain this data in their backups, which is permitted by GDPR regulations; however, any of the data that customers have requested to be removed and flagged for erasure under the “right to be forgotten” clause should never return to a production environment or workflow.
Therefore, before May 2018 and the introduction of GDPR, if the construction company needed to restore a backup including this data, the restore process would be managed in the following manner:
Fast forwarding to May 25, 2018, the next image shows how Veeam DataLabs Staged Restore helps the construction company perform a restore. It shows how they simultaneously remain compliant with GDPR’s Article 17 “Right to be Forgotten,” ensuring the data is successfully restored, but also that all sensitive data included in the backup is effectively removed and therefore never returns to the production environment.
Another prevalent use case often performed by our users is testing and updating patches. Most users prefer to test their patches and roll them out to a production environment with SureBackup. Before Update 4, users would oftentimes lose their tests and replicate within their production environment. Using Veeam DataLabs Staged Restore, this action can be done as part of the restore, with changes within the production environment, therefore removing a redundant step.
Veeam DataLabs Secure Restore
Like compliance, we know that malware is also a major concern. In 2017, there was a significant increase in press coverage around the security of private and sensitive data, most of which was due to the increased threat of ransomware. More data was lost or stolen in the first half of 2017 (1.9 billion records) than in ALL of 2016 (1.37 billion) and that was before the most significant breaches of the year (Source: Breach Level Index).
And the truth is, malicious attacks won’t stop any time soon. Ransomware attacks are predicted to continue in frequency and aggression as they become more sophisticated and harder to stop, and this issue has proven to be top-of-mind for Veeam customers. In fact, a recent ESG study indicated that 70% of our customers are concerned about their backups being contaminated (Source: ESG Master Survey Results, 2018 Data Protection Landscape Survey, October 2018).
Ransomware is a form of malicious malware that takes systems and data hostage, either by locking the user out completely or locking files so they can’t be accessed. The most common action by hackers is to encrypt files and force users to pay a ransom via cryptocurrency to get the decryption key.
Typically delivered through a link, ransomware is usually activated once a user clicks a link, which makes it possible for the virus to take over and spread to the rest of the corporate network.
The customer is then given instructions on how to send payment. Other, more aggressive forms of ransomware exploit security holes to infect systems. NotPetya and WannaCry were two such attacks this year.
It’s important to note that Veeam DataLabs Secure Restore does not prevent ransomware or other malicious attacks. However, this unique, patent-pending capability allows for a pre-staging scan from third-party, anti-virus integrations. This means that when a customer attempts to recover their files, they can verify that their backups are safe and virus-free before recovering, ultimately ensuring the threat has been removed from their network.
For ease of articulating this and the associated issues and problems, the diagram below depicts a typical timeline when a customer is hit with a zero-day attack. Currently, the biggest problem in the industry is that anti-virus vendors lack an adequate fix for a zero-day attack.
In this common timeline example, how do organizations know how much and which data has been compromised and unreadable?
With Update 4, as an added optional step for all non-granular restores inside the restore wizard, Veeam DataLabs Secure Restore will allow customers to scan backups before restoring them to production. The wizard will also include additional options if an infection is identified.
For additional assurance, this process allows for the mount server’s anti-virus software to be fully up to date with virus definitions, and multiple anti-virus vendors can perform a scan.
In the diagram above, you can see that the initial step is to select the restore point required on the Veeam management server. When the backup file is located, disks for the infected machine(s) are mounted to the Veeam mount server. The next stage then allows the anti-virus software to perform a scan against the attached disk.
As part of the recovery wizard, you then have three response options:
- If no infections are found, you can continue with the restore
- If an infection is found, but you need to proceed, Veeam will disable the network adapters for further investigation
- If an infection is found, you can abort the recovery
This feature provides organizations the ability to recover back to a safe, uncompromised backup restore point. The ability to pinpoint the time of infection or the time it was infected and working back from that point allows for a safe and secure process for recovering data after a malicious attack.
Conclusion
With new, stringent compliance standards to follow and aggressive malware concerns weighing heavily on the minds of your key decision makers, Veeam DataLabs can help provide peace of mind that you are following every precaution to remain compliant and avoid the potential of cross-contaminating your production environment with viruses in your backups. Read more on Veeam DataLabs now or download a FREE trial of NEW Veeam Availability Suite 9.5 Update 4 to try Veeam DataLabs today.