- Veeam Support Knowledge Base
- Invalid role for specified account. Status code: Forbidden
Invalid role for specified account. Status code: Forbidden
Cheers for trusting us with the spot in your mailbox!
Now you’re less likely to miss what’s been brewing in our knowledge base with this weekly digest
Oops! Something went wrong.
Please, try again later.
Challenge
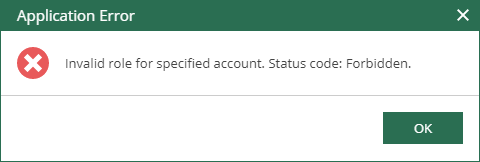
When attempting to add a custom role in the Veeam Backup for AWS console, the following error occurs:
Invalid role for specified account. Status code: Forbidden
Log snippet:
Info [CDefaultAmazonStsInfrastructure] Assuming role 'arn:aws:iam::xyz:role/custom_role'. Error [TryInvokeAsync] Attempt: 1/10. Fail: User: arn:aws:sts::xyz:assumed-role/<SERVER_NAME>-VeeamImpersonationRoleV1-XXXXXXXXXXXX/x-xxxxxxxxxxxxxxxxx is not authorized to perform: sts:AssumeRole on resource: arn:aws:iam::xxxxxxxxxxxxx:role/custom_role
Cause
Solution
If this KB article did not resolve your issue or you need further assistance with Veeam software, please create a Veeam Support Case.
To submit feedback regarding this article, please click this link: Send Article Feedback
To report a typo on this page, highlight the typo with your mouse and press CTRL + Enter.
Spelling error in text
Thank you!
Your feedback has been received and will be reviewed.
Oops! Something went wrong.
Please, try again later.
You have selected too large block!
Please try select less.
KB Feedback/Suggestion
This form is only for KB Feedback/Suggestions, if you need help with the software open a support case
Thank you!
Your feedback has been received and will be reviewed.
Oops! Something went wrong.
Please, try again later.